AWS Data Encryption Strategies Securing Data at Rest and in Transit

Content for Introduction to AWS Data Encryption goes here. This section will cover in-depth details, best practices, examples, and actionable insights about ‘introduction to AWS data encryption’ in the context of AWS management and security. It will also highlight how data encryption helps protect against potential insider threats by ensuring that sensitive data remains secure […]
AWS CloudTrail The Cornerstone of Security Monitoring

Content for Introduction to AWS CloudTrail goes here. This section will cover in-depth details, best practices, examples, and actionable insights about ‘introduction to AWS CloudTrail and Virtual Private Cloud (VPC)’ in the context of AWS management and security. Why CloudTrail is Essential Content for Why it is Essential goes here. This section will cover in-depth […]
How to Secure Your AWS Environment with IAM Policies

Content for Introduction to IAM in AWS goes here. This section will cover in-depth details, best practices, examples, and actionable insights about ‘introduction to iam in aws’ in the context of AWS management, security, and Web Application Firewall. Principle of Least Privilege Content for Principle of Least Privilege goes here. This section will cover in-depth […]
Top 10 AWS Misconfigurations & Security Best Practices to Avoid Them

Content for Introduction goes here. This section will cover in-depth details, best practices, examples, and actionable insights about ‘introduction’ in the context of AWS management, AWS security groups, and common AWS Misconfigurations. Understanding AWS Misconfigurations Content for Understanding AWS Misconfigurations goes here. This section will cover in-depth details, best practices, examples, and actionable insights about […]
AWS Security and Management Comprehensive Guide to Best Practices

AWS Management & Security goes here. This section will cover in-depth details, best practices, examples, and actionable insights about ‘introduction to aws management & aws security in the context of AWS management and security, with practical references to the AWS Management Console for better understanding and implementation. Why AWS Security is Critical Content for Why […]
The Role of Ethical Hacking in Website Security: How Pen Testing Protects Your Business

Cyber threats are constantly evolving, and traditional security plugins alone aren’t enough. That’s where ethical hacking comes in. Also known as penetration testing, it helps you find vulnerabilities before attackers do through a proper vulnerability assessment process. If you run a WordPress site or handle sensitive client data, this proactive approach can be a game-changer […]
Ultimate Guide to WordPress Security Protecting Your Website Made Easy
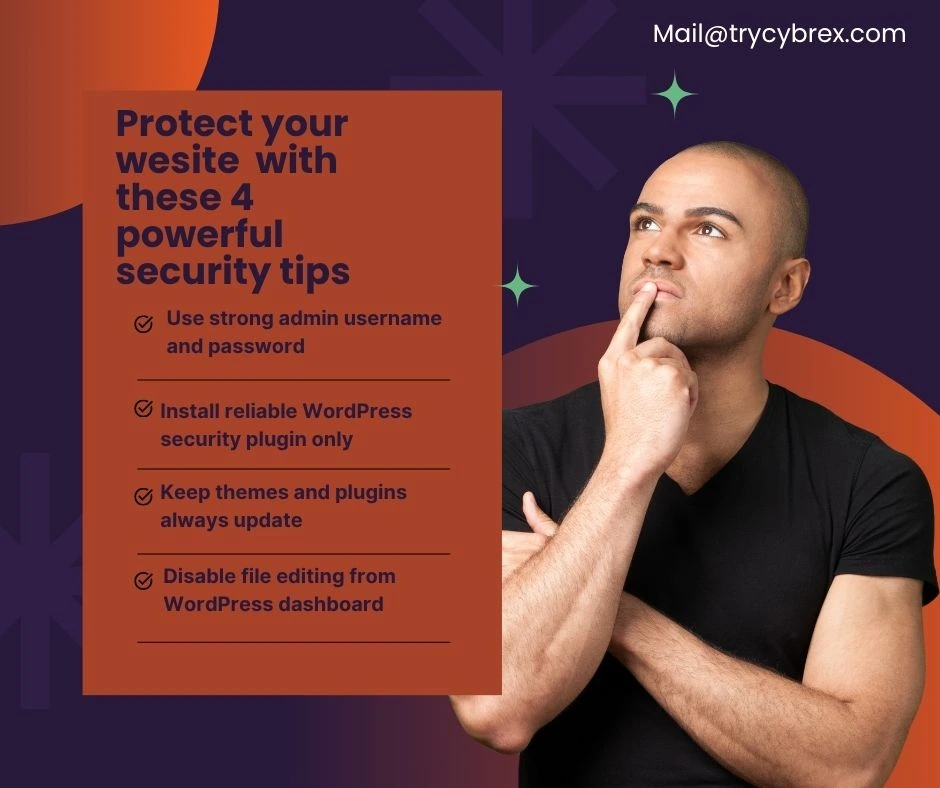
WordPress powers over 40% of websites on the internet, making it a popular target for hackers. Whether you’re using traditional hosting or deploying your site through platforms like Cloud Google, securing your WordPress website is essential to safeguard your digital presence and protect sensitive data. In this guide, we’ll cover everything you need to know […]
The Ultimate Guide to Open Source Intelligence (OSINT) Changing the Game in 2025

Open Source Intelligence (OSINT) is the practice of collecting and analyzing publicly available data to uncover valuable insights for various purposes, including security, investigations, and business intelligence. Professionals using OSINT tools often rely on secure platforms like Cloudflare CDN and Cloudflare DNS to ensure reliable access, performance, and protection while gathering and managing data. OSINT […]
Protect Your WordPress Site from SocGholish Malware Complete 2025 Security Guide

SocGholish malware, also known as FakeUpdates, is a sophisticated and persistent threat that has been targeting websites since 2017. Cybercriminals exploit vulnerabilities in web systems, using this malware to trick users into downloading and executing malicious files by pretending to be legitimate browser updates. This highlights the critical importance of information security in protecting your […]
Top WordPress Security Tips for Australian Websites in 2025

Australian websites increasingly rely on WordPress, the world’s most popular content management system (CMS), powering millions of sites globally including many in Australia. While WordPress offers great flexibility and ease of use, it is also a common target for cybercriminals. In 2025, securing your WordPress website is crucial, especially as cyber threats evolve, including the […]
